Hello Metaspike Community - we have a request to collect emails from SendInc. Has anyone run into this before and were you able to come up with a way to collect the emails?
Here is their documentation for reference:
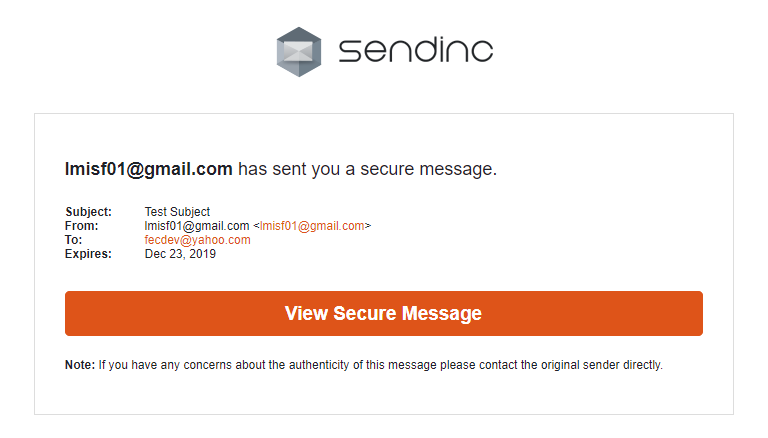
I created a test account and sent a test email. The recipient gets a hyperlink that directs them to Sendinc to log in and view the contents of the message as in the screenshot below:
As per their API documentation, I also tried the Copy Me option to see if that would result in the unencrypted message being sent to the sender. This results in the sender getting a copy of the message, but again, as a link to log into Sendinc rather than as a real message that can be acquired.
So far, no sign of any connectivity options for email clients or a bridge such as the ProtonMail Bridge.
Looking into their API documentation a bit more, I’ve found that you can download a message through Sendinc’s REST API if you know its ID. The Sendinc message ID can be found via the URL in the View Secure Message button, or by checking the X-Sendinc-Message-Id header field in the sent message.
Once you know the message ID (let’s say it is <messageID>), you can request it from the REST API as follows (<username> and <password> are the credentials for the Sendinc account which has access to the message):
curl -u <username>:<password> https://rest.sendinc.com/message/<messageID>.json > Z:\Message.json
If you would like a PDF copy, just append ?pdf=1 as below:
curl -u <username>:<password> https://rest.sendinc.com/message/<messageID>.json?pdf=1 > Z:\Message.pdf
This is something that could ultimately be built into FEC, but I see many gaps in Sendinc’s REST API that would prevent the full spectrum of FEC capabilities from being implemented. For instance, I don’t see a method to list all of the messages associated with an account. Also, the output is not a proper RFC 5322 message.
So, for the time being, your best bet might be to scrape the IDs and make requests against the Sendinc REST API.
P.S. If you are on Windows, you can get curl from here:
https://curl.haxx.se/download.html